The Browser Is the New Enterprise Operating System. Acium Secures It.
SaaS, web apps, AI tools, and agentic workflows all run through the browser, bringing AI-boosted phishing, supply chain extension implants, chatbot data leaks, and unmanaged device access with them. Acium gives you in-session visibility, ICF-powered coherence detection, and unified control across the browsers your teams already use.


The Security Layer That Lives Where Work Lives
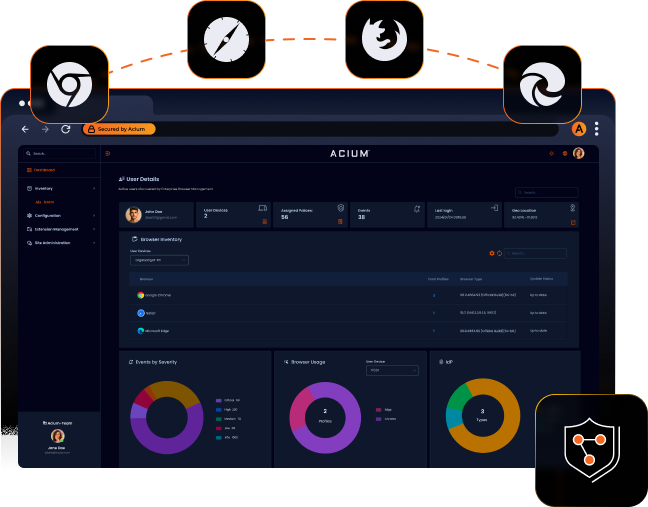
The in-session visibility layer that EDR, SWG, DLP, CASB, and SASE cannot provide
Unified control for Chrome, Edge, Firefox, and Safari from a single console
ICF-powered coherence detection stops AI-boosted phishing and zero-day style attacks
Extension Governance: ICF-powered ERS turns supply chain risk into managed territory
AI interaction governance: stop sensitive data from leaving the browser into unauthorized AI tools
Built for the Browser. Designed for the AI Threat Era.
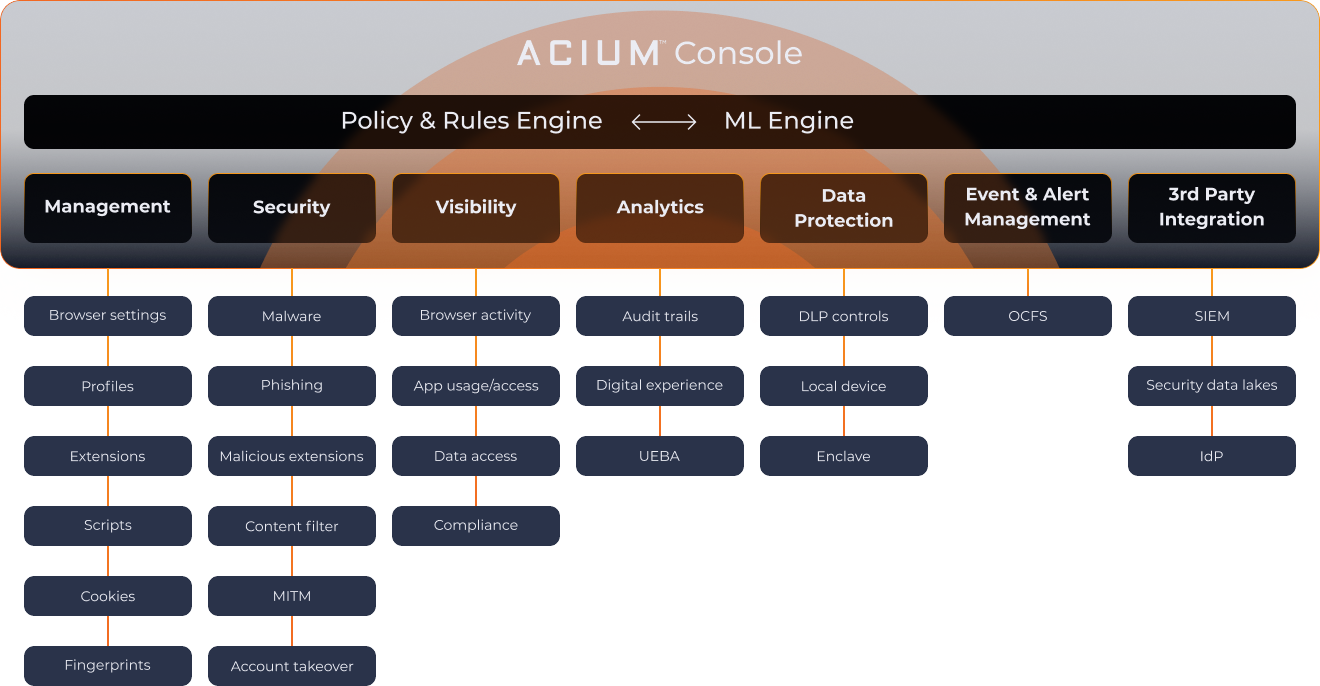
Acium's unified platform closes the browser security gap with ICF-powered coherence detection, deep in-session visibility, and true enforcement, invisibly protecting your data on the browsers your teams already use.
ICF validates the logic, volume, and permissions of every browser action, detecting structural incoherence that stops AI-boosted phishing, malicious extensions, and session attacks that pattern matching cannot recognize.
- Coherence-based detection against AI-boosted phishing and zero-day style attacks
- ICF-powered Extension Risk Scoring (ERS): behavioral and structural analysis
- Real-time event and alert management with OCSF-standard telemetry
Security
ICF validates the logic, volume, and permissions of every browser action, detecting structural incoherence that stops AI-boosted phishing, malicious extensions, and session attacks that pattern matching cannot recognize.
- Coherence-based detection against AI-boosted phishing and zero-day style attacks
- ICF-powered Extension Risk Scoring (ERS): behavioral and structural analysis
- Real-time event and alert management with OCSF-standard telemetry
Pattern Matching Is Over. Welcome to the Coherence Era.
For three decades, security detection relied on recognizing known threats: signatures, blocklists, and behavioral rules built from past attacks. AI ended that era. When attackers can generate novel threats at machine speed, pattern matching falls behind by design. Incoherent Coherence Fingerprinting (ICF) takes a different approach: instead of asking "have we seen this before?", it tests the mathematical coherence of every browser action, stopping zero-day style threats on first contact.
The Pattern Matching Era
Signatures · Blocklists · Behavioral Rules
- ✗Blind to novel threats: requires prior exposure to detect
- ✗Falls behind machine-speed threat generation
- ✗High false negative rates against AI-crafted attacks
The ICF Coherence Era
Logic · Volume · Permissions · Coherence
- ✓Detects structural incoherence on first contact, no prior exposure required
- ✓No signature database. Coherence is the detection mechanism.
- ✓Continuously validates every browser action in real time
Extension Risk Scoring (ERS)
ICF-powered behavioral and structural analysis of every browser extension, exposing supply chain implants and malicious capabilities that signature scanning will never catch.
Phishing & Session Attack Detection
AI-boosted phishing bypasses every filter built on known patterns. ICF validates the coherence of page behavior, credential flows, and session interactions, stopping attacks on first contact.
Expanding to the Full Browser Surface
ICF continuously validates every browser action: SaaS interactions, AI tool usage, agentic workflows, and extension behavior, as the browser becomes the primary enterprise operating system.
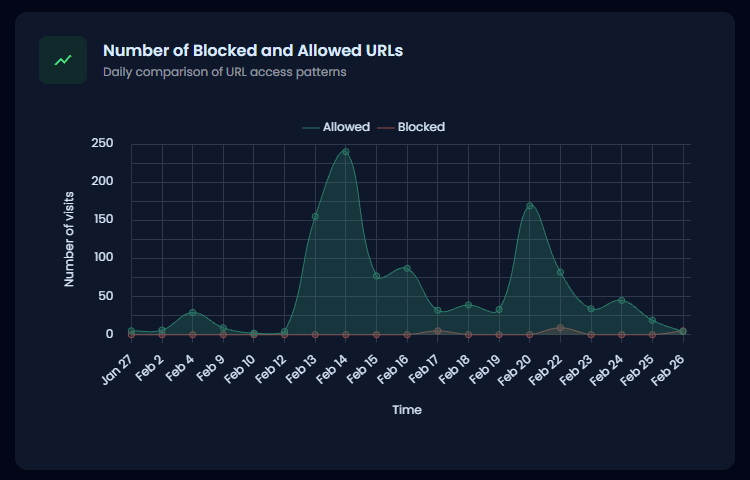
From Zero Browser Visibility to Full Control, in Minutes
Deploy Acium to thousands of users in minutes with zero infrastructure management and immediate in-session visibility. Close the browser security gap while reducing IT overhead and strengthening your compliance posture.
ICF-Powered Threat Detection
Coherence-based validation stops AI-boosted phishing and zero-day style attacks that signatures and behavioral patterns cannot recognize.
Operational Efficiency
Consolidate browser management for 5:1 FTE efficiency with zero infrastructure to manage.
Extension Governance
Automated risk scoring and granular capability control for every browser extension.
Unified Compliance
Real-time visibility into SaaS usage and AI tool interactions for total audit control.
Unified Intelligence, Fragmented Risk Defeat
Acium’s sensor-based architecture provides the depth of an endpoint tool with the agility of a browser tool.
Frequently Asked Questions
Ready to Close the Browser Security Gap?
Start securing your workforce in the AI Threat Era today.
Ready to Close the Browser Security Gap?
Start securing your workforce in the AI Threat Era today.
RESOURCES
Explore the latest resources.
Discover Acium's technical documentation, solution briefs, and thought leadership articles to help your organization strengthen security and productivity.
Acium Data Sheet
Get detailed insights into Acium's capabilities and technical specs with our data sheet.
LEARN MORE→Acium Solution Brief
Explore Acium's features and benefits in our comprehensive solution brief.
LEARN MORE→Taming Browser Extensions: How Unified Browser Security™ Enhances Security Beyond Native Controls
Learn how Acium's new extension management features provide enterprise-grade security and control across browsers while maintaining productivity. Try Unified Browser Security today.
February 04, 2025READ MORE→How Browser Extensions Could Be the Trojan Horse in Your Organization
Discover how browser extensions pose security risks to businesses and how Unified Browser Security™ can help protect your data and workflows.
January 18, 2025READ MORE→